Replica' the Most Unnverving Detective Game Out There
Phone snooping makes for a great detective game, but also a horrifying reality.
Consider all the data most of us pour into our smartphone — passwords, appointment schedules, personal info, selfies — and wonder what would happen if you ever get your smartphone stolen and broken into. The debate about smartphone privacy is so important that Apple went into a public battle with the FBI to protect smartphone data. The data in a smartphone is valuable, and a new game by South Korean indie developer, Somi Games, contextualizes that value in an Orwellian, political thriller called Replica.
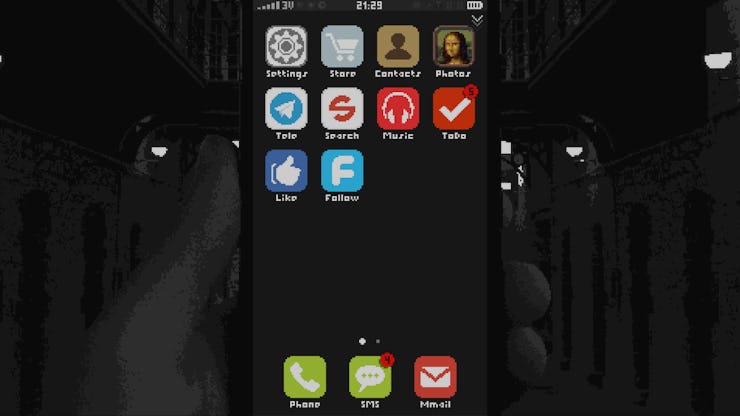
Replica takes place completely on a smartphone screen. That doesn’t mean the game is for smartphones, but instead that the player interfaces with a digital smartphone through a computer screen. From the opening moments, the player is tasked with breaking into this replica smartphone, and given commands by an unknown overseer to snoop through the phone and ascertain whether or not the owner of the phone is a terrorist.
Through interacting with the phone, hacking into the phone’s social media accounts, private photos, SMS, and phone contacts, the player gathers clues on the personality of the owner. It’s actually quite ingenious how information is gathered through all the little bits and pieces of data located in a phone. For instance, a text message from the owner’s mother congratulating him on his birthday let’s the phone voyeur deduce both the password to unlock the phone, as well as the owner’s birth date and age. Imagine all the little bits of information that is passed between you and loved ones through text messages, and suddenly the phone contains much more information than what you consciously put into it.
Lock Screen
When we think about what it means for a smartphone to get hacked, we understand there are specific consequences. Running down recent news headlines we know that a smartphone breach can lead to terrorist inquiries on one end of the public spectrum, and leaked nude selfies on the other end. Both result in serious harm and damage to either the public or individuals, and are understood as serious incidents when it comes to smartphone privacy. However you stand on the debate politically, the results of a smartphone hacking are serious and clearly demand attention.
Consider however, what the government or outside parties can do with the passive parts of your smartphone usage. Perhaps these outside parties get access to the Facebook or Twitter app on your phone. Then they have access to the sites that you share online, what and how you comment to the news, and what posts you like from others. Location tracking on phones reveal what places you visit the most, or what route you prefer to take on your way home. Slowly but surely a profile begins to develop well beyond the simple personal photographs or account passwords.
Social Media App, "Follow"
Replica chose the terrorist plot line as a way to contextualize the dangers of what a rogue government can glean from a smartphone, but the game raises some serious questions about smartphone privacy. Not only for the people who get their privacy breached, but also for the people who breach said privacy.
While playing Replica, I often found myself delighted at each new bit of information I successfully mined from the phone in my possession. The game rewards data mining quite cleverly. Your handler demands you download a ficitonal app called To-Do which not only reports every action- from opening an app to scrolling through photos- to Homeland Security; but it also sends you objectives from your boss.
The insidiousness of this app cannot be overstated. Not only do apps like these exist in real-life, but the objective completion rewards denouncement and spying. While the game bluntly references the Red Scare and McCarthyism, the game genuinely fosters a sense of reward for every bit of personal information reported, and that’s dangerous.
Privacy
The significance of the game’s origin as a South Korean developed title isn’t lost on me. In the post-Korean war era, South Korea saw an unimaginable amount of government abuse, from disappearances of dissidents to Communist witch hunts. But clearly with the United States’ own recent crusade against the likes of Edward Snowden and Apple, this allegory is quickly becoming universal.
And this is just from a political context. With incidents like “The Fappening”, which was an organized hack into iCloud that stole hundreds of nude celebrity selfies, there are voyeuristic connotations to digging around a smartphone. The possibility that a smartphone can provide, not just quantifiable data, but intimate and revealing information offers both a thrill and motive to venture into the depths of a stolen smartphone.
"Under Censorship"
Replica ultimately operates on video game logic. Gather clues, solve the mystery, and win the game. But even if the condition of victory wasn’t dangled in front of the player, the game is designed to the point that for the first time, anyone can understand the “value” of hacking into a smartphone. Whether or not the owner is a terrorist is ultimately irrelevant. Replica is more interested in showing the player the “prize” so to speak, or what it is that can be taken from a smartphone. While professional hackers have always known what’s at stake when they breach into a phone, public perception to smartphone security is still lacking. That’s a huge problem as these phones become more and more ingrained into our everyday lives.
Suddenly, selfies and incriminating phone histories become the least of our worries. For residents in democratic countries, the argument is contextualized into matters of public safety and personal privacy, but in other countries these are matters of life and death. With Donald Trump inciting crowds to denounce their untrustworthy neighbors, Replica is 1984 for the smartphone age. And it’s absolutely terrifying.