Why Deep Root's Leak of 198 Million Voters' Data is a Very Big Deal
The GOP-backed analytics firm left a terabyte of data on a public cloud server.
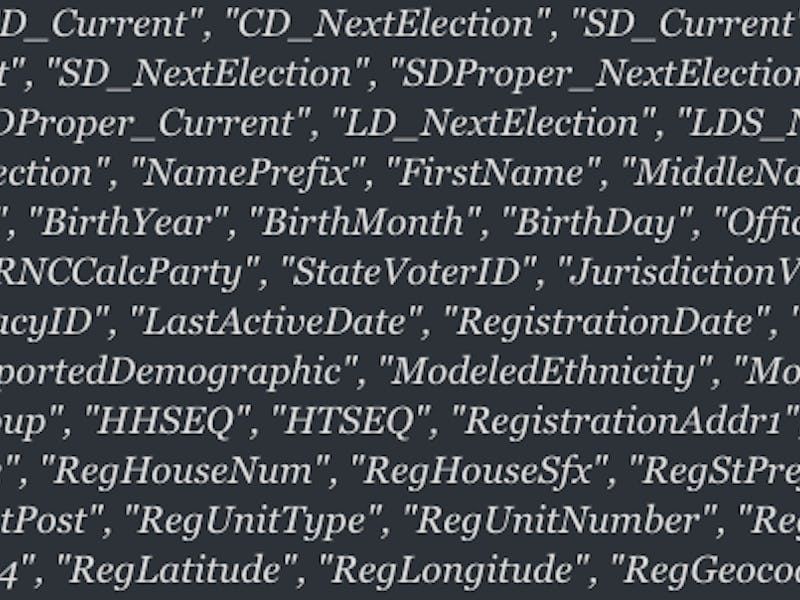
Home addresses, phone numbers, suspected religious affiliation, ethnicity, and where a person stands on hot button issues like abortion and gun ownership are just some of the bits of information amassed on nearly 200 million Americans by the Republican data firm Deep Root Analytics. Then stored it in a publicly accessible Amazon cloud server.
The personal data mother lode — the most of its kind ever exposed — was amassed by Deep Root through a series of sources, including other Republican-allied data firms, super PACs, and even subreddits like r/fatpeoplehate, a thread frequented by posters to the Trump-supporting r/The_Donald. As a media analytics firm, Deep Root uses advanced algorithmic modeling to compile or predict the political preferences of any registered voter that’s been caught in its extensive web.
A security researcher who has “Data breach hunter” in his Twitter bio discovered the trove of data last week.
The leak — if you can even call it that, the URL was publicly accessible — sheds light on the complex, multi-million dollar enterprise of collecting American citizens’ personal details. While this kind of data collection sounds insidious, it’s a reality that contributed to the 2016 election of Donald Trump. To be fair, it was a reality during the Obama era too; as targeting potential voters — especially in swing states — can make or break an election.
What is not normal is leaving over 61 percent of the population’s personal data out in the open to be accessed by anyone. With an investigation into Russian meddling in the 2016 election currently underway, negligent seems like an understatement when it comes to this kind of privacy malpractice.
According a statement provided to Gizmodo, Deep Root claims the 1.1 terabytes of personal information was publicly accessible for 12 days due to a security update. In other words, this data was not even leaked due to hacks — it was just out there on the internet waiting to be found by someone who happened to look.
That someone turned out to be Chris Vickery, a cyber risk analyst at UpGuard who works with a research team to find these kinds of exposures and then alert the public. Vickery discovered on June 12 that the server could be accessed by anyone who found the URL, without a password.
UpGuard reports that Vickery alerted federal authorities and the server was secured two days later.
So far, Deep Root doesn’t believe its proprietary data was accessed by any malicious third parties during the 12 days that the data was exposed on the open web. That’s reassuring. What isn’t is the fact that it was out there in the first place.