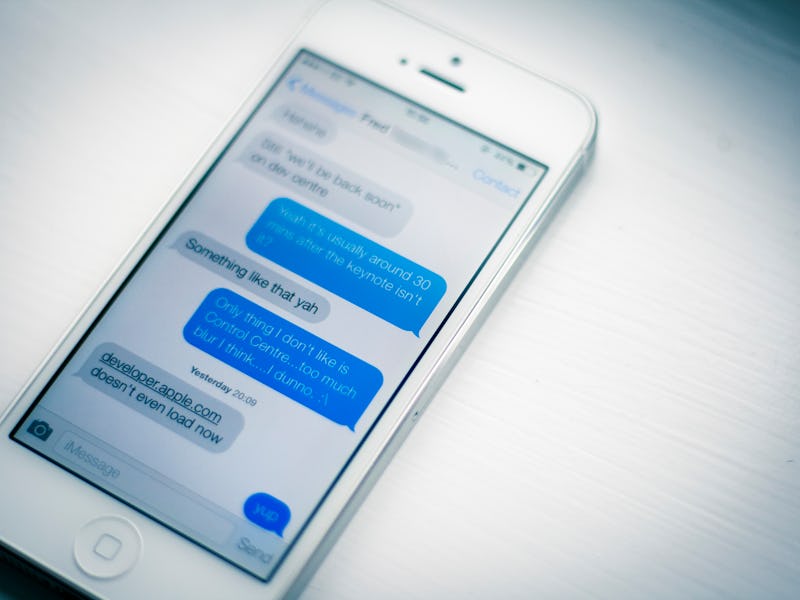
Researchers Find New iPhone Exploit That Hacks iMessage Photos and Videos
Apple is forced to take emergency action.
Apple’s vaunted encryption may not be as tough as the company wants you to believe.
A team of researchers at Johns Hopkins University has discovered a way to access encrypted pictures and videos sent through iMessage while they are in transit between two devices. While the 9.3 security update begins to address the problem, phones will only be patched once they are running the newest version of iOS due to be released today.
The researchers found that it was possible to guess the key to encrypted photos and videos. Apple required only a 64-digit key to access the secure files stored on the iCloud servers, and the team was able to crack the code within a few months. It is precisely the kind of weakness governments are capable of exploiting, because the work of guessing takes more brute force than anything else.
Matthew D. Green, a computer science professor at Johns Hopkins University who led the effort, believes that the ease with which his graduate students broke into Apple’s servers highlights the need to avoid weakening encryption further by building “backdoors” for government surveillance.
“Even Apple, with all their skills — and they have terrific cryptographers — wasn’t able to quite get this right,” Green told The Washington Post. “So it scares me that we’re having this conversation about adding backdoors to encryption when we can’t even get basic encryption right.”
The dispute between the FBI and Apple has become the most high-profile skirmish in the encryption debate.
The long-running debate about whether the government should have access to encrypted communication on third-party devices has recently achieved renewed intensity since the FBI asked Apple to help the law enforcement agency to break into the locked iPhone of the San Bernardino terrorists. Apple CEO Tim Cook has flatly rejected to aid the FBI, and the case will be heard in federal court this week.
The particular exploit Green’s team discovered would not help the FBI access the San Bernardino iPhone, particularly because the law enforcement agency doesn’t know exactly what it’s looking for. But the discovery does raise the question of why Apple should build new exploits into its devices when plenty already exist. Apple certainly seems to prefer Green’s researchers to the government’s warrants.
“We appreciate the team of researchers that identified this bug and brought it to our attention so we could patch the vulnerability. . . . Security requires constant dedication and we’re grateful to have a community of developers and researchers who help us stay ahead,” Apple said in a statement.
Ahead is one of looking at it, Apple. They also said your security kind of sucks, and that anyone with a little time could break your devices. If that’s the best we have, maybe we really do have a problem.