How the US Can Protect Its Electrical Grid From Russian Hackers
The number of potential targets only continues to grow.
The US electricity grid is hard to defend because of its enormous size and heavy dependency on digital communication and computerized control software. The number of potential targets is growing as “internet of things” devices, such as smart meters, solar arrays, and household batteries, connect to smart grid systems.
As researchers of grid security, we believe that current security standards mandated by federal regulations provide sufficient protection against observed threats. But recent incidents demonstrate the ongoing challenge of ensuring everyone follows the guidelines, which themselves must change over time to keep up with technological shifts.
The threat is real: In late 2015 and again in 2016, Russian hackers shut down parts of Ukraine’s power grid. In March 2018, federal officials warned that Russians had penetrated the computers of multiple US electric utilities and were able to gain access to critical control systems. Four months later, the Wall Street Journal reported that the hackers’ access had included privileges that were sufficient to cause power outages.
Specific technical details have not yet been made public, so it’s hard to know exactly what the hackers did or gained access to. What has been revealed is that these breaches were accomplished with common hacking techniques, such as sending spearphishing emails to specific employees. Apparently, and reassuringly, the US attacks didn’t involve more advanced techniques seen in the Ukraine incidents, including custom-made software to target specific systems.
In addition, human errors will inevitably lead to mistakes that will weaken the security of some of the thousands of digital devices needed to protect the grid. And more sophisticated attackers may still find and exploit currently unknown vulnerabilities. Therefore, it’s important for electric utilities, grid operators, and vendors to remain vigilant and deploy multiple layers of defense.
Major Players Have Some Protections
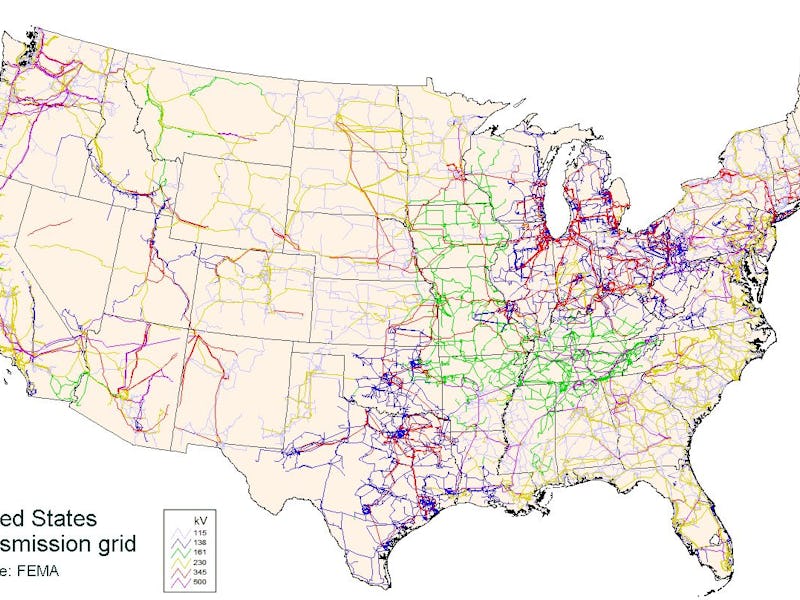
There are two main aspects to grid architecture that need defending in different ways. The first element is the bulk power system, often referred to as the “transmission grid.” It connects high-capacity power plants, transmission wires, and substations that collectively generate and transport huge quantities of electricity over hundreds or thousands of miles. The rest of the grid is made up of smaller distribution grids — connected with the bulk power system — delivering electricity to homes and businesses around the country. The strongest standards for protection apply only to the bulk power system; though many distribution systems follow the same guidelines, they remain optional.
US federal rules, as well as those set by the agency that governs the North American grid — which also includes large parts of Canada — require companies operating elements of the bulk power system to follow certain basic cybersecurity measures, including monitoring their networks to detect intrusions and mandating two-factor authentication for user logins.
Many large utilities do even more, assessing their risks in standardized ways and practicing responses to computer intrusions. These exercises often include hundreds of companies and organizations rehearsing how to collaborate to detect and confine attacks and restore service to customers.
Smaller Companies Are More Vulnerable
Because transmission grid utilities should already have some protections against network intrusions, it is likely that the Russian hackers looked elsewhere, infiltrating smaller distribution utilities. If that’s so, any potential power shutdown or other problems in those systems would be confined to smaller areas — like towns or cities. That, in turn, means fewer customers would be affected, with less work needed to get power back on.
But it highlights a worrying reality: Smaller and midsized companies that operate electricity distribution systems often have inadequate resources to invest in full cybersecurity protections. The more than 3,000 utilities in the US have trouble finding sufficiently skilled workers who understand how the computerized and physical components of the grid work together and how to protect them.
In addition, utilities rely on complex supply chains to provide equipment, software, maintenance, and other business functions. These external contractors and vendors may not implement protections as rigorous as the utilities. And their computer systems often have connections to the utilities’ networks, which may be considered trusted and safe, rather than potential avenues of attack.
Stepping Up Defenses
Fixing all these potential problems is complex. First, all utility companies — even the smallest — should adopt basic security protections like those required of large utilities. Some states are moving to require this of the power companies serving their residents, but many aren’t yet. Further, we recommend all companies that are part of the grid participate in coordinated grid exercises to improve cybersecurity preparedness and share best practices.
In addition, all utility companies need to take steps to ensure the hardware and software they use are from trustworthy sources and have not been tampered with or modified to allow unauthorized users in.
It won’t be enough to protect against today’s threats. Adversaries are likely to employ increasingly sophisticated techniques that exploit both computer and human vulnerabilities. Companies need to ensure they engage in what might be called sustainable cybersecurity — ongoing processes that let systems and staff adapt over time, to stay ahead of the threats.
Researchers have an important role, too, exploring ways that emerging technologies like cloud computing, blockchain, and big-data analytics could help reduce risks without introducing any additional weaknesses. Further, researchers should identify more advanced ways to secure the grid, and reduce these systems’ complexity, which would limit both current risks and future unknowns.
This article was originally published on The Conversation by Manimaran Govindarasu and Adam Hahn. Read the original article here.