Synthetic DNA Enables the Latest Horrifying Cybersecurity Threat
A computer could be infected just by processing DNA.
The electronic and molecular worlds are converging as scientists refine techniques for sequencing and synthesizing DNA (i.e. reading and writing DNA). Synthetic biology is an important field — advancements will help us fight diseases and disorders — but as a research team from the University of Washington demonstrated in a study publicized Thursday, these advancements will also give hackers the chance to write destructive codes into synthetic DNA.
The team identified two major cybersecurity risks: First, that it’s possible to insert malicious software into the strands of synthetic DNA, and second, that synthetic biologists often use programs with security vulnerabilities that would make them susceptible to an attack.
“We wondered whether under semi-realistic circumstances it would be possible to use biological molecules to infect a computer through normal DNA processing,” says study co-author Peter Ney.
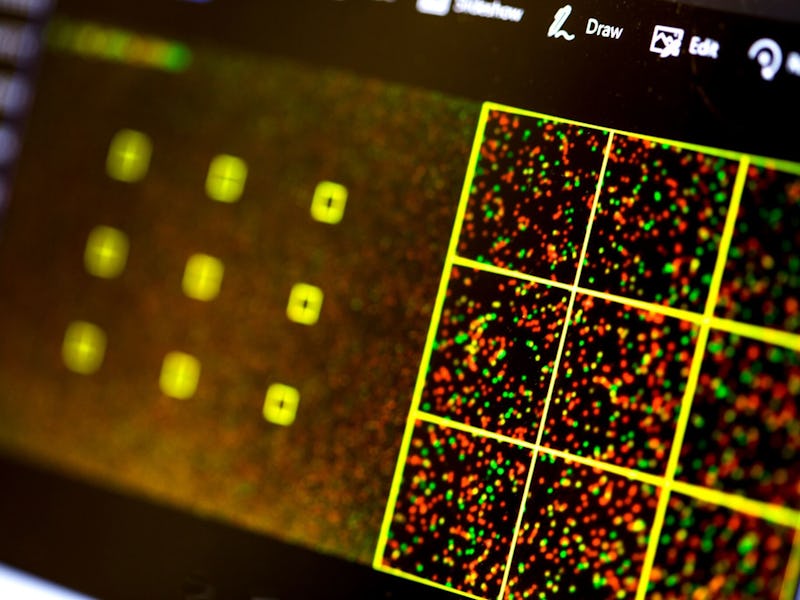
A test tube containing hundreds of billions of copies of the code.
It is possible. Through trial and error, the researchers managed to include an exploit in synthetic DNA strands that could take control of a computer when it processed the strands. If hackers managed to use this technique to infect DNA with the same exploit, they could potentially change test results and gain access to personal information and a company’s intellectual property.
The team also discovered that many of the open-source software programs that researchers use to process data from DNA sequencing contain security weaknesses. Programs that were designed years ago to service scientists on a very small scale are often coded in an unsafe language.
How might attackers go about inserting a malicious code into synthetic DNA? As it turns out, they have a lot of options.
Output from a sequencing machine that includes the team’s exploit, which is being sequenced with unrelated strands. Each dot represents one DNA strand in a given sample.
“A few scenarios come to mind,” co-author Karl Koscher tells Inverse. “First, an existing DNA sample could be contaminated with this malicious DNA. For example, if you want to exploit the computers at a sequencing facility that performs some sort of analysis (a service like 23andme, although to the best of our knowledge, 23andme does NOT sequence your DNA, but performs other types of analysis), you could simply contaminate your own sample that you send to them.”
“Second, because multiple DNA samples are often sequenced together, errors inherent in current sequencing processes will cause some of your malicious DNA data to end up in other people’s data,” Koscher continues. “Third, you might envision a scenario where someone (such as a manufacturer of GMO seeds) wants to prevent others from easily sequencing the DNA in products they sell. Biologically-benign but digitally-malicious code could potentially be implanted to thwart others from analyzing that DNA.”
Researchers have a lot of options to safeguard against these risks, and many of them are standard fixes. For example, even simple software analysis tools can find many security problems and help people determine which elements of programs need to be rewritten.
“One of the big things we try to do in the computer security community is to avoid a situation where we say, ‘Oh shoot, adversaries are here and knocking on our door and we’re not prepared,’” said co-author Tadayoshi Kohno in the press release. “Instead, we’d rather say, ‘Hey, if you continue on your current trajectory, adversaries might show up in 10 years. So let’s start a conversation now about how to improve your security before it becomes an issue.’”