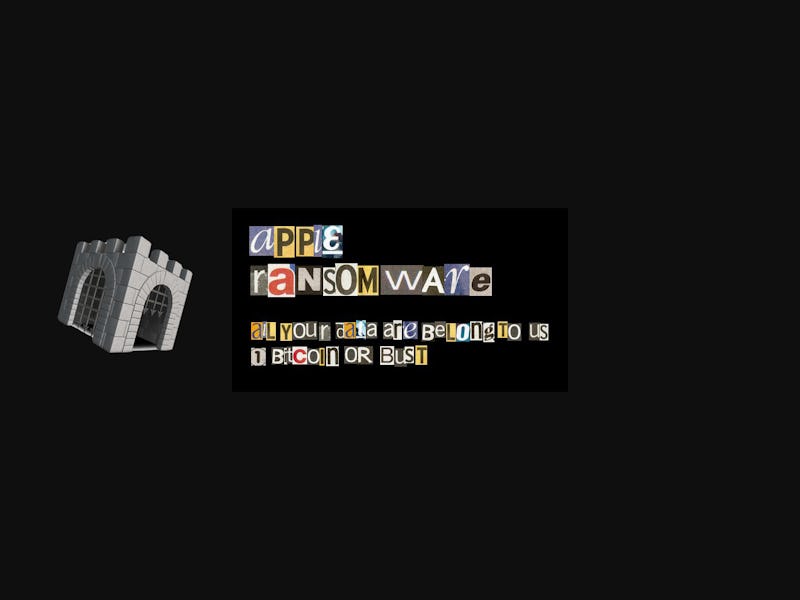
Apple Gets Its First Dose of Ransomware as 6,500 Users Hit with Encryption Virus
"KeRanger" was covertly bundled up with a Transmission update, and the bomb was set to go off at 2 p.m. EST today.
If you were one of the unlucky many on Friday to download and install the new version of Transmission, a torrent downloading application, today is your day of reckoning: Your information, and your very access to your pillar of self, may be put up for ransom.
Mac users have never before been exposed to fully realized ransomware, and for good reason: Apple products have been relative strongholds against viruses. But this installer veiled the malicious program, KeRanger, and gave it a three-day dormancy period. Transmission is one of the more popular, simplistic, and intuitive BitTorrent clients and makes it very easy for users to download torrents, be they torrents of albums, programs, movies, or etc.
On that fateful third day — which happens to be today — those who installed Transmission version 2.90 and enjoyed three jubilant days of torrented goodness were met with a rude ransom note at 2 p.m. Eastern time: KeRanger encrypted the contents of the unfortunates’ Macs and demanded 1 bitcoin — equivalent, today, to about $409 — to decrypt said data. And with over 300 different types of file extensions encrypted, very little was spared.
John Clay at Transmission gave Inverse a fuller story:
“We’ll be posting a notice in the next few days with more information, but our best guess at this point is that approximately 6,500 infected disk images were downloaded (of tens of thousands of legitimate downloads of this version prior). Of those, our presumption is that many were unable to run the infected file due to Apple quickly revoking the certificate used to sign the binary, as well as updating the XProtect definitions. We’re waiting on confirmation from Apple on that.
“The Sparkle auto-update mechanism was not compromised, and would have failed to update to the infected binary as the hash was different. Further, our third party cache (CacheFly) was not compromised, which is where many of the software update websites link to (MacUpdate et al). We’ve also confirmed that a user with an infected version can successfully auto-update to the legitimate releases of 2.91 or 2.92, with 2.92 actively attempting to remove the malware.”
If you use Transmission, here’s how to check whether your own computer was infected:
- Open up the built-in Activity Monitor in Applications/Utilities.
- Under the “Disk” tab, search for “kernel_service”. (“kernel_task” is innocuous and a vital part of the OSX; if you see that process running, do not panic.)
The ransom note, which is oddly polite given its creators’ indubitably sorry souls, is viewable here. It begins, “Your computer has been locked and all your files has [sic] been encrypted with 2048-bit RSA encryption.”
Transmission responded quickly and updated its installer to exclude and purportedly remove KeRanger from infected computers.
One of the researchers who discovered the ransomware — Claud Xiao — was active spreading the word:
It also warned all who were updating the program:
Apple also responded by removing that version of the installer’s certification — a certification that allowed the ransomware to bypass the normally rigorous GateKeeper and XProtect that keep Macs secure.
Palo Alto Networks exposed the security breach. For the full report and a self-protection guide, look here.