This Old Tweet Raises Questions About Marcus Hutchins' Kronos Charges
Was MalwareTech covering his tracks or just doing security research?
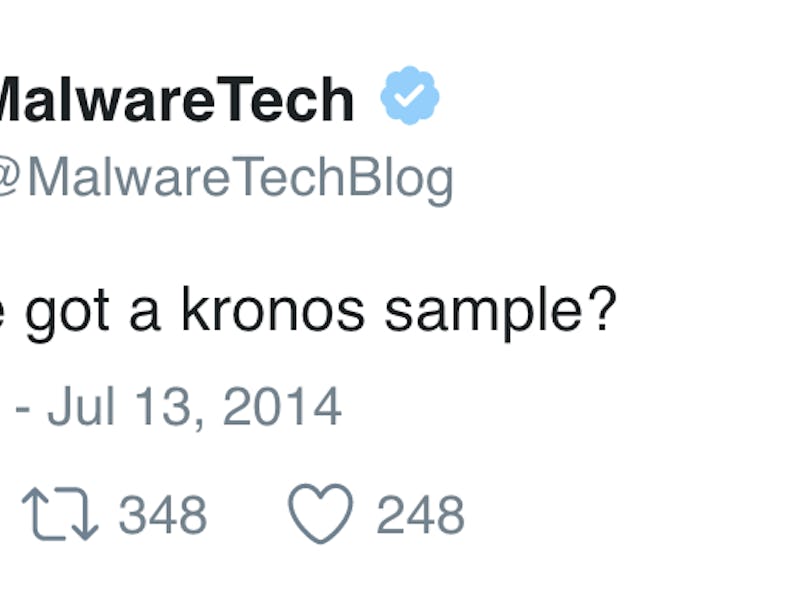
A tweet from 2014 resurfaced on Thursday that shows Marcus Hutchins — aka MalwareTech, the security researcher who accidentally stopped the WannaCry malware attack in May — was looking for a sample of Kronos, a banking malware program.
“Anyone got a kronos sample?” he asked on his Twitter account. There’s just one problem: The FBI thinks Hutchins created the program. He wasn’t merely looking for a sample, alleges the Department of Justice in a sealed indictment filed last month.
And so federal agents arrested Hutchins on Wednesday in Las Vegas as he attempted to fly out of the country after attending the DEF CON hacking conference. His indictment was unsealed after his arrest.
Hutchins, 22, a United Kingdom resident, is alleged to have created and distributed — creation isn’t a crime but distribution would be — the Kronos malware that attacked computers between 2014 and 2016. Kronos was “designed to harvest and transfer the username and password associated with banking websites as they are entered on an infected computer to a control panel hosted on another computer inaccessible to the victim,” in the words of a DOJ press release about the charges.
It was often referred to as a “banking Trojan” because it stole information to hack into banking and financial accounts. It was used until late 2016. Hutchins’s alleged involvement with Kronos occurred between 2014 and 2015.
The Department of Justice isn’t commenting on the old tweet, nor was it acknowledged in the indictment.
“Defendant Marcus Hutchins created the Kronos malware,” reads the indictment. It alleges that his other crimes include: “Advertising the availability of the Kronos malware on internet forums; selling the Kronos malware; receiving and distributing the proceeds obtained from selling the Kronos malware; and acts done in furtherance of the conspiracy were concealed and hidden, and caused to be concealed and hidden.”
Hutchins’s defenders wonder if he could have been mistakenly identified as the Kronos creator, because of his anti-malware security research.
“This could very easily be the FBI mistaking legitimate research activity with being in control of Kronos infrastructure,” security researcher Ryan Kalember told The Guardian. “Lots of researchers like to log in to crimeware tools and interfaces and play around.”
Kalember also said that “sometimes you have to at least pretend to be selling something interesting to get people to trust you. […] It’s not an uncommon thing for researchers to do and I don’t know if the FBI could tell the difference.”
Hutchins posted the tweet on July 13, 2014, around the same time that the indictment alleges that a “video showing the functionality of the ‘Kronos banking trojan’ was posted to a publically [sic] available website.” (That website was AlphaBay.) Hutchins’s alleged partner, whose name is blacked out of the public version of the indictment, “used the video to demonstrate how Kronos worked.”
Hutchins achieved a certain level of internet fame atop his already well-known reputation as a security researcher when he “accidentally” activated the kill switch of the “WannaCry” malware program that spread across 70 countries. The malware exploited software developed by the National Security Agency to hack medical and telecommunication networks in Asia and Europe.
Georgia-based security researcher Jake Williams, who goes by the name @MalwareJake on Twitter, was one of many security researchers online who came to Hutchins’s defense on Thursday, citing the old tweet.
“It’s not a crime to create malware. It’s not a crime to sell malware. It’s a crime to sell malware with the intent to further someone else’s crime,” Orin Kerr, a law professor at George Washington University told Andy Greenberg of Wired. “This story alone doesn’t really fit. There’s got to be more to it, or it’s going to run into legal problems.”
British security researcher Andrew Mabbitt says that Hutchins is currently detained at the FBI’s Las Vegas field office. It is not yet clear how long Hutchins will be there or when a trial will be held.