12 NSA Patents That Prove the Future of National Security Will Be Bizarre
Most, but not all, of the NSA's patents are top-secret. These lunatic ideas make you wonder what they're not telling us.
Whether or not you care that the NSA has archived your personal information in a server farm somewhere and whether or not you live in America, the future of U.S. national security strategy will affect you. And that future will be governed to no small degree by the technologies employed by the NSA, which doubles as a skunkworks for out there monitoring projects and creates patents at an almost industrial pace.
The NSA’s patents do not expire, but they are confidential. Only when someone else attempts to patent the same technology or technique is the existence of an NSA patent rexistence of an NSA patent revealed. Think of it as Mindsweeper for intellectual property. Now, there’s a database (take that, NSA) in which you can find all such exposed patents. It’s a safe bet that this list comprises a minute fraction of all the NSA’s patents, but, like any good sampling, the list gives us a good window into what the evil geniuses are dreaming up.
Below is a highlight reel of those patents, organized into three categories: patents that’d make James Bond feel at home, patents with ridiculous titles, and patents that give us substantial pause.
Secret Agent Style
Some of the patents would be right at home in a James Bond or Batman movie. Q and Lucius Fox have rivals within the NSA, it seems.
Desmond Llewelyn as "Q."
Biomimetic voice identifier
“Current voice identification systems are limited in their ability to efficiently process audio from environments that include high noise content and multiple speakers.”
The conclusion of the patent summary casually states:
“Additionally, the device also includes an artificial neural network and a display means.”
Method of biometric authentication
“Biometrics is the science of identifying individuals based upon physiological or behavioral characteristics. In recent years, automated biometric systems have been developed that can be used to identify, or to verify, the identity of individuals. These systems are now being marketed not just to law enforcement, but to individuals and corporations that need to provide some measure of access control to computer systems or physical facilities. They are also being incorporated into encryption packages that are intended to protect personal files, private information and financial transactions.”
The patent application goes on to explain that, if a hacker can gain access to the system, and therefore the biometric data (which, spoiler alert, they can), the system is quite vulnerable.
“It is an object of the present invention to provide a biometric authentication method that does not allow data stored on the system to be directly reversed to recover the biometric.”
Reusable Tamper Evident Envelope
“Protecting the contents of an envelope from tampering is a very old problem. Historical methods of producing a tamper-evident envelope used a seal imprinted into candle wax to indicate the sender sealed the envelope and no tampering had occurred en route. Since these early methods, more sophisticated methods have developed. It is well known that banks, government agencies, and businesses ship important items from one location to another. For many of these items, the shipper wants to know whether the item has been tampered with after being placed into an envelope or bag. Modern tamper-evident envelopes use a plastic or paper sheet material for the envelope, with a pre-formed seal along all but one marginal edge. After an item is placed inside the envelope, the user activates the user-activated seal, sealing the envelope.
“It is an object of the present invention to provide a reusable tamper-evident envelope with enhanced protection against unauthorized entry.”
Reusable Tamper Indicating Bag Closure
“The present invention is a reusable tamper indicating bag closure that can be used with any bag to transport documents or objects that may contain information that needs to be protected such as portable computing devices, laptops, PDA, mobile phones, iPods . . . etc. This bag closure can be sized to be used with any type of bag. […] The user can choose which securing and tamper-proofing means to utilize depending on the situation.”
Method of Detecting Intermediary Communication Device
“The present invention is a method of detecting the presence of an intermediary communication device in the communication path of a target communication device. The communication device is preferably a computer, but the present invention applies to any other suitable communication device that communicates using different interconnection layers. The communication path is preferably the communication network on which a target communication device operates (e.g., a computer network if the communication device is a computer), but any other suitable communication path is possible.”
(Must be nice.)
Absurd Titles
Some of the patents boast titles that even Kurt Vonnegut couldn’t have dreamt up. The devices and methods that these patents describe probably give the NSA some creepy capabilities, but it’s less frightening and more fun to just laugh at the absurdity of the language.
Magnetic Bubble Logic Apparatus
Hybrid Space/Time Integrating Optical Ambiguity Processor
Method for Bumping a Thin Wafer
Inexplicable Ideas
Finally, there are a few patents that are just incomprehensible. There’s very little that can explain why the NSA thought it worth its time to dream up and then patent these “inventions.”
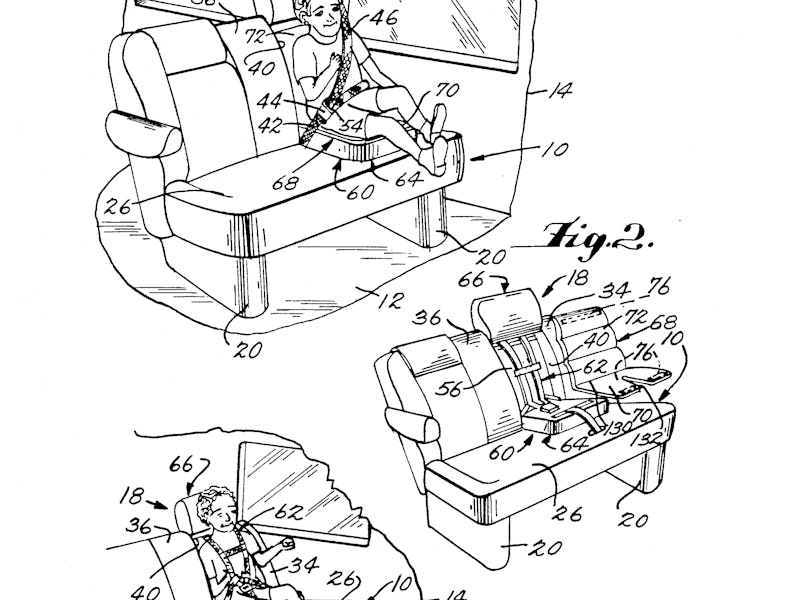
Integrated Child Seat for Vehicle
Game Board
Secure Manhole Accessway
Method of Generating Multiple Random Numbers
“Ask that toddler in the child seat.”