How 2 Prisoners Built Secret Computers and Got Online
How they were caught was so obvious.
Inmates at an Ohio prison managed to build two makeshift computers out of discarded parts and perform a litany of illegal activities for several months before getting caught over an obvious flaw in their plan: bandwidth overages.
A report released last week from the Ohio Office of the Inspector General lays out how in 2015, staff at the Marion Correctional Institution — a medium-security prison in Marion County — discovered two computers hidden in the ceiling of a closet in a training room. The report claims the computers were built piecemeal by two inmates named Scott Spriggs and Adam Johnston, who had acquired the parts through a labor program called RET3 that employs inmates to disassemble out-of-date computer hard drives and other obsolete technology.
Using the stolen credentials of a prison sub-contractor named Randy Canterbury, Johnston was able to connect to the Ohio Department of Rehabilitation and Correction (ODRC) network and also get online. So what exactly do you get up to when you have unlimited secret access to the internet from prison?
The ceiling of a closet where two PCs were discovered.
Cybercrime
Once the PCs were discovered, a forensic analysis of the computers’ hard drives elicited evidence of a slew of downloaded VPN software, tools for finding security vulnerabilities, and password cracking and generally just a “large hacker’s toolkit” for “malicious activity.”
Inmates appeared to be conducting attacks against the ODRC network using proxy machines that were connected to the inmate and department networks.”
Ohio Office of the Inspector General report
Analysis also discovered articles about making homemade drugs, plastics, explosives, and credit cards. “Findings of bitcoin wallets, Stripe accounts, bank accounts, and credit card accounts point toward possible identity fraud, along with other possible cyber crimes,” the report reads.
Identity Fraud
Johnston admitted to investigators that he had accessed a Bloomberg article (maybe this one?) explaining how one can submit fraudulent tax returns and arrange to have the refunds loaded onto debit cards.
Through the Department Offender Tracking System, he found the social security number and date of birth of an inmate whom he had never met named Kyle Patrick and submitted online credit and debit card applications in his name. The cards were to be sent to an address across the street from the house of Johnston’s mother, Karen Gallienne.
According to an interview with Gallienne she believed Johnston was intending to forward her money.
“He was gonna try and put some money on it so he could give me money… help me out.”
Karen Gallienne, mother of inmate Adam Johnston, Ohio Office of the Inspector General report
Hall Passes
Analysis also determined that access passes were granted to multiple inmates, allowing them to gain entrance to various parts of the Marion Correctional Institution. Inmates’ personal information, such as disciplinary records, sentencing data, and locations were also accessed.
And Porn
Johnston also admitted to being responsible for downloading pornography found on a thumb drive in the possession of another inmate. This inmate claimed the thumb drive also contained full movies, TV series and music, which he would then sell to other inmates.
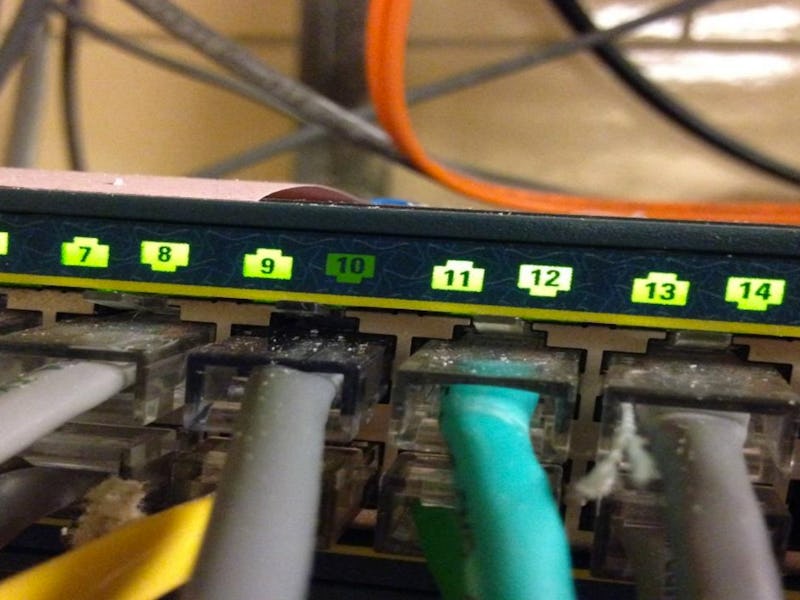
A network hub located in the training room where Ohio prison inmates stored a makeshift computer.
In what feels like a rather anticlimactic twist, what ended up tipping off ODRC to all this nefarious activity was a notification that a computer using Ray Canterbury’s log-in credentials had exceeded its daily bandwidth — on a Friday. Canterbury’s work week was Monday through Thursday.