Mess
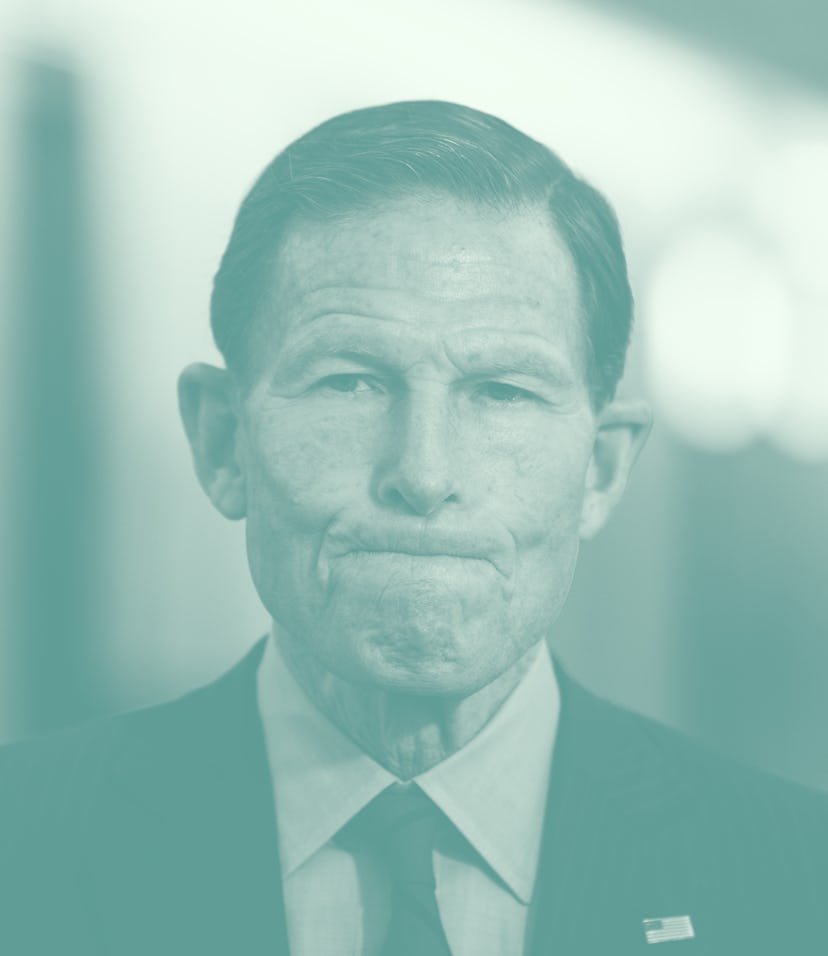
EARN IT Act lawmaker finally admits the bill is targeting encryption
Sen. Blumenthal spent years skirting around the EARN IT Act's anti-encryption clauses. Now he's (kind of) ready to talk about it.
After first being teased in early February, a new version of the highly controversial EARN IT Act has officially been reintroduced to lawmakers. And some of its most fervent advocates are finally being open about their true mission: undermining encryption.
Back when the original EARN IT Act was introduced in 2020, Sen. Richard Blumenthal (D-Conn.) — who co-wrote the bill — did his best to skirt around the issue of encryption entirely, despite its being one of the bill’s main focuses. During hearings about the bill, Sen. Blumenthal consistently pushed for a narrative that EARN IT was not about encryption at all.
“The bill says nothing about encryption. … Big Tech is using encryption as a subterfuge to oppose this bill,” Sen. Blumenthal said at the time.
Now Blumenthal is walking back his words — and not even in a way that admits he’s changed his tune. In an interview cited by The Washington Post, Blumenthal finally addressed the encryption-based elephant in the room. But not in a way that will quell anyone’s concerns.
Oh so now it’s about encryption — The impetus behind the EARN IT Act has always been minimizing child sexual abuse material (CSAM) by holding websites and internet providers accountable for any such material they might host. Under EARN IT, all companies that have built encryption into their customer-facing products would need to build special backdoor access for government use.
During the EARN IT Act’s first time around the legislative branch, Sen. Blumenthal did everything in his power to skirt around the issue of encryption, despite it being a main tenant of the bill. This time he’s addressing it, albeit in a roundabout way.
Speaking to advocates’ worry that companies will be less inclined to implement encryption at all, given that they’d need to create backdoor access, too, Blumenthal said (via WaPo):
… that lawmakers incorporated these concerns into revisions, which prevent the implementation of encryption from being the sole evidence of a company’s liability for child porn. But he said lawmakers wouldn’t offer a blanket exemption to using encryption as evidence, arguing companies might use it as a “get-out-of-jail-free card.”
If this doesn’t make much sense to you, that’s likely because it doesn’t really make much sense at all. Blumenthal is no longer pretending the encryption bit in the bill is meaningless, but he’s still unwilling to address the serious threats it proposes.
Here’s one more peek at how Blumenthal is still attempting to skirt around the bill’s encryption issues in an even more roundabout fashion (from an EARN IT markup session:
That’s the key distinction here. Doesn’t prohibit use of encryption, doesn’t create liability for using encryption, but the misuse of encryption to further illegal activity is what gives rise to liability here. That’s the very simple answer…
Not like this — Rather than simply denying the encryption issue at all, this time around Sen. Blumenthal is doing everything he can — up to and including spewing nonsense sentences — to minimize the encryption clause’s impact. Activists and internet experts aren’t ready to just let him get away with it.
Encryption services have grown in popularity over the last few years as our understanding of them as a necessary part of safe, private communications has risen to prominence. Creating explicit backdoor access would undermine the entire project of encryption; the whole point is that no one can see it except those communicating with each other.
Major advocacy groups like the Electronic Frontier Foundation (EFF) are working overtime to raise awareness of the bill’s implications.
“State legislatures will have unprecedented power over websites, both large and small, and will likely pressure companies to scan not only messages, but cloud storage, online photos, and entire websites,” the EFF writes on its action page. “This requirement will put encryption providers in an awful conundrum: either face the possibility of losing everything in a prosecution or costly litigation, or undermine their users’ security, making all of us more vulnerable to online criminals.”
Somehow the EARN IT Act manages to be even more problematic than its anti-encryption clauses. As an almost direct successor to SESTA/FOSTA — the 2018 bill that was meant to limit sex trafficking on the internet — the EARN IT Act brings with it the possibility of similarly dire consequences. (SESTA/FOSTA has had a ripple effect that’s deplatformed countless sex workers and disproportionately affected LGBTQ communities.)